Cybersecurity in shipping and port technologies: examples of cyber attacks in maritime
Cybersecurity of AIS, ECDIS, VDR, EPIRB and other specific information systems for shipping companies and technologies in the maritime Industry.
Shipping, like any other large field of activity, develops in parallel with the course of technological progress: ships increase in size, while crews decrease, as more and more processes are becoming automated. Nowadays, some onboard systems receive updates while sailing, the teams have Internet access. Along with the growing reliance on automation, the risk of external interference and disruption of key systems is greatly exacerbated; hackers can interfere with the operation of the ship or navigation systems, cut off all external communications of the vessel, or obtain confidential data. But many people employed in the maritime sector are accustomed to being part of an "almost invisible" industry, invisible to the common man, so not all information about successful attacks is widely publicized: often business owners can keep silent about it, fearing such consequences as loss of image, claims from outside clients and insurance companies, initiating investigations by third parties and government agencies.
In any case, surveys of the cybersecurity of facilities in the maritime sector are quite acute. In order to continue the conversation about the cybersecurity of shipping, we will review specific information systems and technologies in maritime. Thus, the risks of cyber threats will be obvious.
AIS is an automatic identification system. It serves to transmit the vessel's identification data (including its cargo), current position and course. It is also used to prevent collisions of ships, monitor their condition and with its help, the owner can monitor his ship. It also provides communication between courts. The device works by transmitting signals in the VHF band between ships, floating repeaters and coastal AIS gateways that are connected to the Internet. All vessels on international voyages, vessels of over 500 gross tonnage, and all passenger liners must be equipped with AIS. The system works on marine search and rescue equipment.
In any case, surveys of the cybersecurity of facilities in the maritime sector are quite acute. In order to continue the conversation about the cybersecurity of shipping, we will review specific information systems and technologies in maritime. Thus, the risks of cyber threats will be obvious.
AIS is an automatic identification system. It serves to transmit the vessel's identification data (including its cargo), current position and course. It is also used to prevent collisions of ships, monitor their condition and with its help, the owner can monitor his ship. It also provides communication between courts. The device works by transmitting signals in the VHF band between ships, floating repeaters and coastal AIS gateways that are connected to the Internet. All vessels on international voyages, vessels of over 500 gross tonnage, and all passenger liners must be equipped with AIS. The system works on marine search and rescue equipment.
is an electronic cartographic navigation information system that collects and uses AIS messages, data from radars, GPS and other vessel sensors (from a gyrocompass) and compares them with embedded maps. It is used for navigation, automation of certain tasks of the navigator and increasing the navigational safety of navigation. The system usually consists of a workstation (or two for monitoring and for course planning) connected to the ship's sensors and instruments, on which the ECDIS software is installed.
VDR (Voyage Data Recorder)
- flight data recorder, flight recorder, analogue of the "black box" used in aviation. The main tasks are to record important voyage information of the vessel, including both technical and heading data, as well as voice recordings from the captain's bridge, and its preservation in case of an emergency.
ECDIS (Electronic Chart Display and Information System)
is an emergency radio beacon, a transmitter that, upon activation, gives a distress signal, the transmission of which, depending on the technology, can be carried out via satellite, in the VHF band, or in combination. In addition to the distress signal, some EPIRBs can also transmit vessel information (when synchronized with AIS).
collects data from the ship's sensors and transmits them for decision making to the captain's mosik and/or to the dashboard of the shipping company manager. Vessel telemetry data from engine sensors, shaft, fuel tanks and others is analyzed to prevent technical problems of the vessel, as well as to save fuel. Such systems allow you to quickly respond to emergency situations and take preventive measures.
EPIRB (Emergency Position Indicating Radio Beacon)
is a system that allows tracking the movement of containers using GPS and, less often, other data transmission channels. Most of the companies in this field also offer tracking devices for other areas, for example, personal trackers for tourists, solutions for vehicle tracking, etc.
is a system that simplifies the communication and interaction of port services, ensuring the handling when entering a port. Thanks to the port management system, the vessel will stand for less time and the port will be able to receive more vessels. The system accompanies the vessel from the moment the agent is nominated and the first notifications of port calls are sent.
CTS (Container Tracking System)
System vulnerabilities in cyber attacks in the maritime industry
Research carried out in the past few years, as well as information on incidents that have nevertheless become available to a wide range of people, only confirms concerns about the safety of the maritime sector.

Cybersecurity of Automatic Identification System (AIS)
A large study on AIS security was conducted by researchers at Trend Micro. The research results were presented at the Black Hat Asia 2014 conference. Two attack vectors were considered: the first - against AIS providers collecting data from AIS gateways installed on the coasts to collect AIS information and then to provide commercial and free services in real time.
The second type of attack is at the radio transmission layer, that is, the AIS protocol itself. The attack on the protocol was carried out using SDR (software-defined radio). The architecture of the protocol was developed a long time ago, mechanisms for validating the sender and encrypting the transmitted data were not provided, since the likelihood of using expensive "iron" radio equipment to compromise the technology was regarded as low. Research has shown the following scenarios are possible:
- changes in ship data, including its position, course, cargo information, speed and name;
- creation of "ghost ships", recognized by other ships as a real ship, in any location in the world;
- sending false weather information to specific vessels to force them to change course to avoid a nonexistent storm;
- activation of false collision warnings, which can also cause automatic correction of the course;
- the ability to make an existing vessels "invisible";
- creation of non-existent search and rescue helicopters;
- falsification of EPIRB signals, which activate alarms on nearby ships;
- the possibility of carrying out a DoS attack on the entire system by initiating an increase in the frequency of transmission of AIS messages.
In addition, it is worth noting that the vessel's personnel can turn off their AIS, becoming "invisible" (according to CyberKeel, a fairly common practice for passing dangerous sections of the water area, such as the Gulf of Aden, the "fiefdom" of Somali pirates), and in some cases change the broadcast information manually.
Plotting a nonexistent warship of country A on AIS maps in the territorial waters of country B could provoke a diplomatic conflict. In addition, an attack by an intruder can also lead to deviating from the course as a result of spoofing messages about a possible collision with it or to "luring" to a certain point in the water area by creating a false signal of an emergency beacon.
- changes in ship data, including its position, course, cargo information, speed and name;
- creation of "ghost ships", recognized by other ships as a real ship, in any location in the world;
- sending false weather information to specific vessels to force them to change course to avoid a nonexistent storm;
- activation of false collision warnings, which can also cause automatic correction of the course;
- the ability to make an existing vessels "invisible";
- creation of non-existent search and rescue helicopters;
- falsification of EPIRB signals, which activate alarms on nearby ships;
- the possibility of carrying out a DoS attack on the entire system by initiating an increase in the frequency of transmission of AIS messages.
In addition, it is worth noting that the vessel's personnel can turn off their AIS, becoming "invisible" (according to CyberKeel, a fairly common practice for passing dangerous sections of the water area, such as the Gulf of Aden, the "fiefdom" of Somali pirates), and in some cases change the broadcast information manually.
Plotting a nonexistent warship of country A on AIS maps in the territorial waters of country B could provoke a diplomatic conflict. In addition, an attack by an intruder can also lead to deviating from the course as a result of spoofing messages about a possible collision with it or to "luring" to a certain point in the water area by creating a false signal of an emergency beacon.
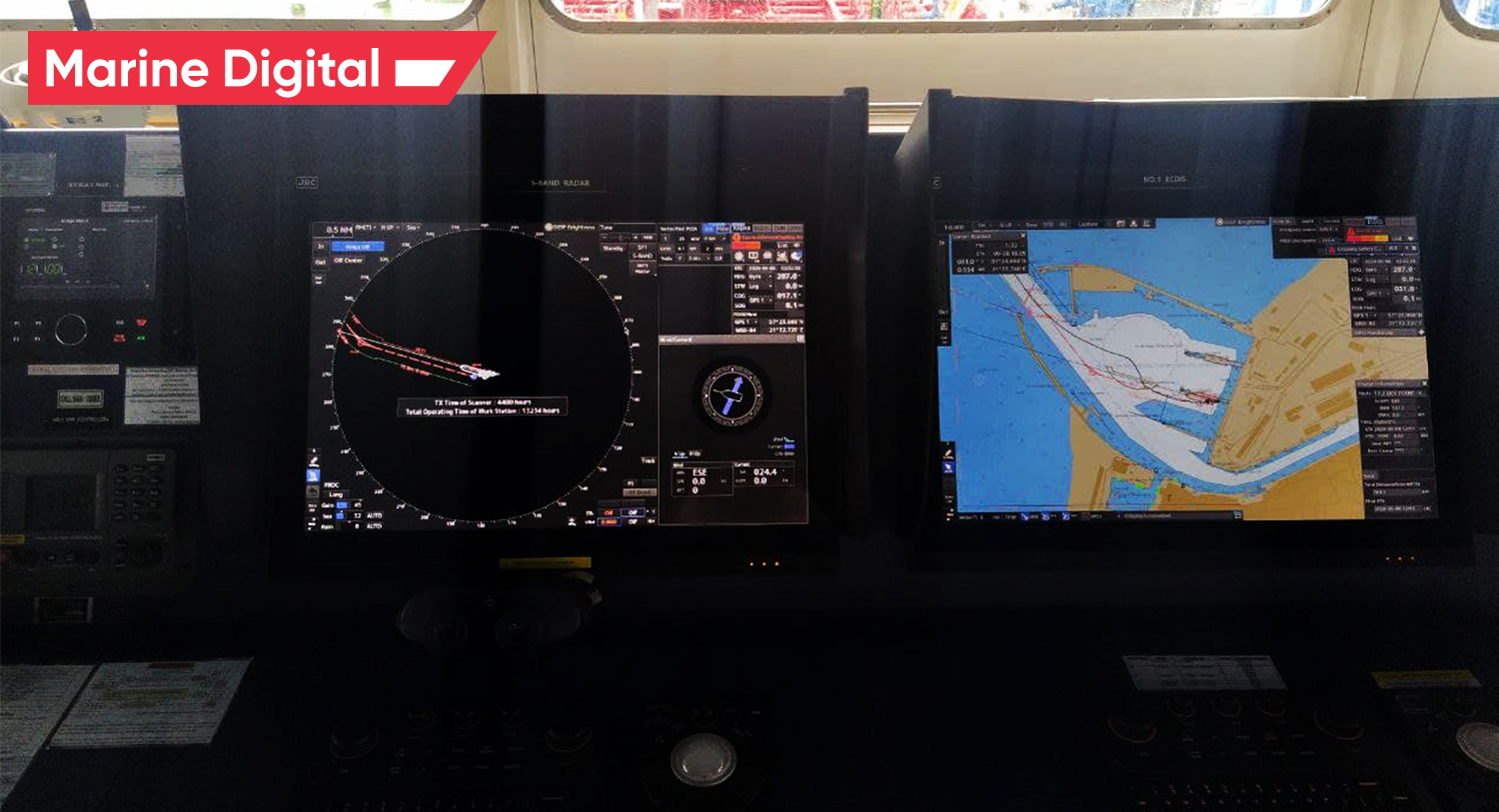
Cybersecurity of ECDIS (navigation system)
On March 3, 2014, the NCC Group released a report on the security of ECDIS systems. The report presented the results of a study of the system of one of the leading vendors. It is noted that the majority of systems of this class are a set of applications installed on a workstation running Windows operating systems (often XP) and located on the bridge of the ship. Other systems are connected to the workstation with ECDIS, via the on-board LAN network, from which the Internet is most often available: NAVTEX (navigation telex, a unified transmission system for navigation, meteorological and other line information), AIS, radars and GPS equipment, as well as other sensors and sensors.
Correct operation of the ECDIS system is very important, its compromise can lead to the most unfavorable consequences - injuries and even death of people, environmental pollution and large economic losses. A "frozen" vessel, having lost the ability to navigate correctly, will block a busy canal or gateway for an indefinite period, which, under certain circumstances, will cause huge economic losses. A tanker carrying oil or other chemical products and running aground due to navigation errors is a ready-made scenario for an environmental disaster.

Cybersecurity of Voyage Data Recorder (VDR)
The data obtained from the device is extremely important in the investigation of incidents, accidents and disasters that occurred at sea. The VDR is analogous to the aircraft's "black box" but it is orange.
On February 15, 2012, Marines aboard the Italian private tanker Enrica Lexie, tasked with protecting the vessel from a possible pirate attack, mistakenly opened fire on an Indian fishing vessel and killed two Indian citizens. The tanker's flight recorder lost data from sensors and voice recordings for the period of time when the incident occurred. There were two versions of the reason for what happened: the overwriting of data by the VDR itself and the deliberate destruction of evidence. The loss of data naturally complicated the investigation, which gave rise to a diplomatic conflict between India and Italy and ended only on August 24, 2015.
A couple of weeks after the events at Enrica Lexie, on May 1, 2012, a Singaporean freighter Prabhu Daya rammed a fishing boat off the coast of India, in the Kerala region, and fled the scene. As a result of the collision, three fishermen were killed. An interesting detail emerged in the press following the Indian law enforcement investigation: During the arrival of the officials on the Singapore ship, one of the members inserted a USB stick into the VDR; this led to the erasure of all files and voice recordings from him. Later, despite all the efforts of the experts, the data could not be restored.
The Enrica Lexie and Prabhu Daya cases clearly reflect that deleting data on the VDR can make it extremely difficult or completely deadlocked an investigation into an incident at sea. Moreover, if attackers have the ability to edit data on the recorder and substitute them, there is a high probability of organizing a fraud, which will send the investigation into the wrong direction.
A couple of weeks after the events at Enrica Lexie, on May 1, 2012, a Singaporean freighter Prabhu Daya rammed a fishing boat off the coast of India, in the Kerala region, and fled the scene. As a result of the collision, three fishermen were killed. An interesting detail emerged in the press following the Indian law enforcement investigation: During the arrival of the officials on the Singapore ship, one of the members inserted a USB stick into the VDR; this led to the erasure of all files and voice recordings from him. Later, despite all the efforts of the experts, the data could not be restored.
The Enrica Lexie and Prabhu Daya cases clearly reflect that deleting data on the VDR can make it extremely difficult or completely deadlocked an investigation into an incident at sea. Moreover, if attackers have the ability to edit data on the recorder and substitute them, there is a high probability of organizing a fraud, which will send the investigation into the wrong direction.

Cybersecurity of Port Management and Terminal Operating System
Port Information Systems are undoubtedly the most complex and extensive IT structures in shipping. "If you saw one port, you saw one port" is a common phrase, because each port as a whole and from the point of view of information systems is unique. However, it says a lot about the fact that very little attention is paid to port cybersecurity.
US Coast Guard Commander Joseph Kramek writes in his monograph on cybersecurity in major US ports: "Of the six ports tested, only one had a cybersecurity risk assessment; no port had an incident response plan in this area. What's more, of the $ 2.6 billion in port protection grants created after September 11, 2001, less than $ 6 million was spent on cybersecurity projects. " Other risk factors noted by the author are the maintenance of some systems by companies not related to the port, the work of employees from their devices, and the lack of practice in conducting cybersecurity briefing among personnel.
US Coast Guard Commander Joseph Kramek writes in his monograph on cybersecurity in major US ports: "Of the six ports tested, only one had a cybersecurity risk assessment; no port had an incident response plan in this area. What's more, of the $ 2.6 billion in port protection grants created after September 11, 2001, less than $ 6 million was spent on cybersecurity projects. " Other risk factors noted by the author are the maintenance of some systems by companies not related to the port, the work of employees from their devices, and the lack of practice in conducting cybersecurity briefing among personnel.
The most famous port cyber security incident occurred in the port of Antwerp in 2012. The short scheme, according to which the smuggling was delivered to Europe, was as follows: in the containers in which registered and duly issued goods arriving from Latin America were transported, smuggled goods (mainly drugs and weapons) were loaded at the port of departure. Upon arrival in Europe, the gang's "IT department" intercepted the 9-digit PIN codes used to conduct container operations on DP World systems. These codes are required for handling port loading and unloading systems. After the smuggled container arrived in Antwerp, the smugglers, connected to one of the port's wireless networks, instructed the loading systems to move the "charged" container onto their truck before the owner arrived. Operational work, which began following complaints from companies about the periodic loss of containers, led to a series of searches and raids in Denmark, the Netherlands and Belgium. Weapons, cash and cocaine were found, fifteen people were detained.
Cybersecurity of CTS, GPS and satellite communication systems
The maritime industry is actively using SATCOM (Satellite Communications) satellite technologies for Internet access, ship-to-ship and ship-to-land communications, GPS / DGPS for location and navigation, and tracking of transported goods.
Satellite communication systems (SATCOM), including those connecting vessels via the Internet with each other and with the mainland, contain a large number of vulnerabilities, according to the IOActive report. Inspection of satellite terminals used in shipping and in other sectors (aviation, military) and manufactured by leading companies in the industry (Harris, Hughes, Cobham, JRC, Iridium) revealed critical security holes such as devices using unsecured or even undocumented protocols , factory-set up accounts, the ability to exploit the password reset function, backdoors. However, all confidential information obtained in the course of audits and studies, including technical aspects and procedures for conducting audits, as well as information on the possibilities of exploiting vulnerabilities, after its transfer to vendors and regulatory commissions, was not made publicly available.
Another significant case of satellite systems being compromised occurred in July 2013. Students from the University of Texas at Austin were able to divert a yacht worth $ 80 million from course using equipment that did not cost more than $ 3,000.Using a GPS signal simulator (used, for example, when calibrating equipment), duplicating the signal of a real satellite and by gradually increasing the power, they were able to "persuade" the ship's navigation system to accept the spoofing device's messages and discard the signal of the real satellite as interference. After the navigation system began to orient itself according to the data of two satellites and the attacking device, the researchers managed to deviate the vessel from the original course.
Satellite communication systems (SATCOM), including those connecting vessels via the Internet with each other and with the mainland, contain a large number of vulnerabilities, according to the IOActive report. Inspection of satellite terminals used in shipping and in other sectors (aviation, military) and manufactured by leading companies in the industry (Harris, Hughes, Cobham, JRC, Iridium) revealed critical security holes such as devices using unsecured or even undocumented protocols , factory-set up accounts, the ability to exploit the password reset function, backdoors. However, all confidential information obtained in the course of audits and studies, including technical aspects and procedures for conducting audits, as well as information on the possibilities of exploiting vulnerabilities, after its transfer to vendors and regulatory commissions, was not made publicly available.
Another significant case of satellite systems being compromised occurred in July 2013. Students from the University of Texas at Austin were able to divert a yacht worth $ 80 million from course using equipment that did not cost more than $ 3,000.Using a GPS signal simulator (used, for example, when calibrating equipment), duplicating the signal of a real satellite and by gradually increasing the power, they were able to "persuade" the ship's navigation system to accept the spoofing device's messages and discard the signal of the real satellite as interference. After the navigation system began to orient itself according to the data of two satellites and the attacking device, the researchers managed to deviate the vessel from the original course.
Cybersecurity of Vessel Performance Monitoring system
As the example of the vessel performance monitoring and fuel optimization system by Marine Digital, we will highlight the case of cyber security, which includes secure data collection, transmission and its storage.
Marine Digital FOS is a cloud-based system hosted at Amazon facilities in compliance with cybersecurity requirements.
Marine Digital FOS is a cloud-based system hosted at Amazon facilities in compliance with cybersecurity requirements.
AWS IoT Core provides automated configuration and authentication upon a device's first connection to AWS IoT Core, as well as end-to-end encryption throughout all points of connection so that data is never exchanged between devices and AWS IoT Core without a proven identity.
AWS IoT Device Defender audits device-related resources (such as X.509 certificates, IoT policies, and Client IDs) against AWS IoT security best practices (e.g., the principle of least privilege or unique identity per device), continuously monitors our device fleets to detect any abnormal device behavior that may be indicative of a compromise by continuously monitoring high-value security metrics from the device and AWS IoT Core (e.g., the number of listening TCP ports on your devices or authorization failure counts).
Marine Digital FOS box (hardware part, which installed on a vessel) consists of a Data Collection Unit (DCU), a power supply, and a GSM modem, all-in-one robust enclosure, interfacing with the sources of input signals via a read-only NMEA connection, that pulls in data integrated sources, encodes and records it to the integrated storage, and then uploads the collected data to the cloud data lake when a GSM connection is available, autonomously from the shipboard systems. So there is no way to access the equipment on board.
Find more information about the issue of the safety of connecting and exchanging information when implementing Marine Digital FOS, or write to us hello@marine-digital.com
AWS IoT Device Defender audits device-related resources (such as X.509 certificates, IoT policies, and Client IDs) against AWS IoT security best practices (e.g., the principle of least privilege or unique identity per device), continuously monitors our device fleets to detect any abnormal device behavior that may be indicative of a compromise by continuously monitoring high-value security metrics from the device and AWS IoT Core (e.g., the number of listening TCP ports on your devices or authorization failure counts).
Marine Digital FOS box (hardware part, which installed on a vessel) consists of a Data Collection Unit (DCU), a power supply, and a GSM modem, all-in-one robust enclosure, interfacing with the sources of input signals via a read-only NMEA connection, that pulls in data integrated sources, encodes and records it to the integrated storage, and then uploads the collected data to the cloud data lake when a GSM connection is available, autonomously from the shipboard systems. So there is no way to access the equipment on board.
Find more information about the issue of the safety of connecting and exchanging information when implementing Marine Digital FOS, or write to us hello@marine-digital.com

TOP 5 factors contributing to lower fuel costs for Shipping companies
Get a presentation with a full description of the features and free pilot project with trial of Marine Digital FOS for 2 months
"Clicking the button, you consent to the processing of personal data and agree to the privacy policy"

Get an overview "The Pathway to Zero Carbon Shipping:
IMO Compliance and CII Optimization through SEEMP" on email and download it for FREE! Leave your email now!
"Clicking the button, you consent to the processing of personal data and agree to the privacy policy, as well as consent to subscribe to the newsletter. "
Аdvantage of Fuel Optimization System from Marine Digital:

Marine Digital FOS can be integrated with other system and third-party's solutions through the API. To implement vessel performance monitoring for any vessel, we are using mathematical algorithms, machine learning and the same equipment as in FOS. The more data we collect from vessels, the more precise reports and recommendations our system will perform according to your individual requirements in fleet management.
If you have any questions about the solutions and the Marine Digital System platform, write to us, we will be happy to answer
If you have any questions about the solutions and the Marine Digital System platform, write to us, we will be happy to answer
Increased business process speed
Reducing to zero the number of errors

Best offer to the clients

Reduction in operating expenses
Have a questions?





